 I remember a sweet, simple time, when I didn’t know I had to think about password security – I had 1 password that was 7 characters with an easily remembered word that I used for everything. Heck, my email account wouldn’t allow MORE than 8 characters. Of course, there was no online banking or ecommerce and the GDP of entire Eastern European nations didn’t depend on the illicit revenue derived from hacking, phishing and scamming.
I remember a sweet, simple time, when I didn’t know I had to think about password security – I had 1 password that was 7 characters with an easily remembered word that I used for everything. Heck, my email account wouldn’t allow MORE than 8 characters. Of course, there was no online banking or ecommerce and the GDP of entire Eastern European nations didn’t depend on the illicit revenue derived from hacking, phishing and scamming.
But the reality of this age is that we must protect our bank accounts, our email, our cloud storage, our social media accounts, even our identities from people who pay their rent by selling our information on the dark web.
Have I been pwned?
The list of companies whose databases of client credentials have been stolen grows every day and includes such common companies as Forbes.com, LinkedIn.com, Dropbox.com, Adobe.com, MySpace.com, AshleyMadison.com, Yahoo.com, Last.fm, Experian and on and on. We all do, or have done, business with these companies. The exposed identities in this country alone number in the tens of millions. And some of us have been exposed multiple times.
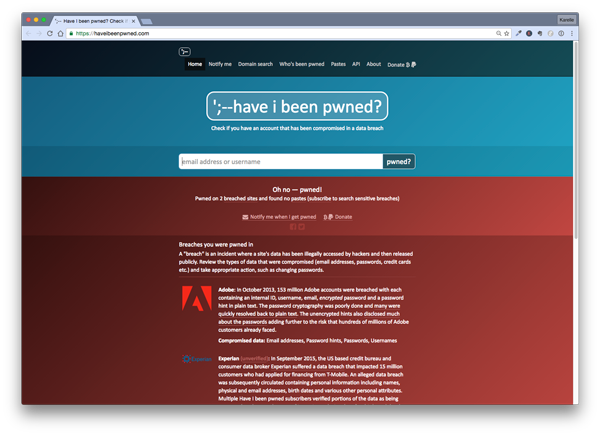
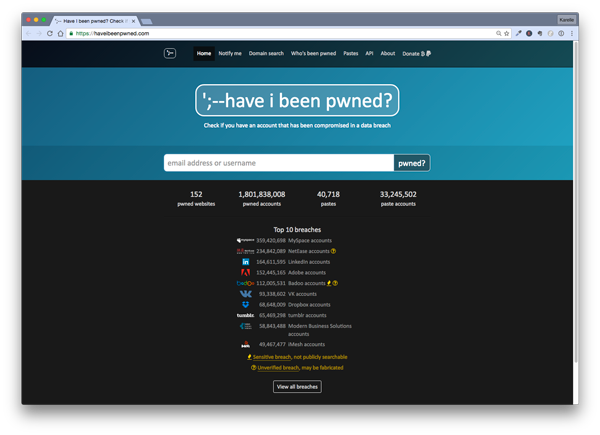 Fortunately there are ways to find out if your email address(es) have been part of one of these known thefts. The best one is https://haveibeenpwned.com/, a free website to check and see whether any email has been part of a hacked database, or in geek parlance, been pwned (yes I know I wrote pwned – it can be pronounced poned, pawned, or even owned). Another freemium site (email checks are free, but you can also check by other kinds of data for a monthly subscription) is https://www.leakedsource.com/ . If you find your email on one of these, you should act immediately.
Fortunately there are ways to find out if your email address(es) have been part of one of these known thefts. The best one is https://haveibeenpwned.com/, a free website to check and see whether any email has been part of a hacked database, or in geek parlance, been pwned (yes I know I wrote pwned – it can be pronounced poned, pawned, or even owned). Another freemium site (email checks are free, but you can also check by other kinds of data for a monthly subscription) is https://www.leakedsource.com/ . If you find your email on one of these, you should act immediately.
 So your password security has been compromised, what to do
So your password security has been compromised, what to do
The very first thing you should do is to change the password at the site where you’ve been pwned. Just saying “I’ll never use that account again” is not enough. Go change the password. Then go and change the password on any site where you used the same password. We’ll get back to this in a bit.
Then if the original site is a financial site or ecommerce, make sure no transactions have been made for which YOU can’t account. If they have, you need to get in touch with the company immediately, either by phone or using an email address intended to report theft or abuse and report the breach.
After that go read this article on how to clean up after a hack. Sorry. It’s going to take work to regain your password security.
How to NOT be hacked – better password security
- The number one rule of password security is to NEVER REUSE PASSWORDS. I’ll wait while you roll your eyes and groan.
Almost everyone I know – clients, family, friends, people I talk to while standing in line – has reused passwords. Including me. But that’s a hacker’s wetdream. All they have to do is to crack one password and they have gained entrée into a big chunk of your online life. Even if you think your password is pretty darn strong (and we’ll get to that in another sec), you’re increasing the odds that you’re going to be victimized if you reuse passwords. Even using 3 different strong passwords is not sufficient. Additionally the cleanup is significantly harder if you have the same password for a bunch of sites. - Second make your passwords painful for the hacker’s software to crack. The more you make the hacker’s computer work to crack your password, the more likely they’ll give up before they get there. I have seen a lot of benchmarks for what constitutes a difficult password, but experts agree that more than 12 characters, preferably more than 16, increases the odds that it would take too long and makes your password secure. Current thinking is that a series of 3-4 dictionary words that appear after rank 10000 in this list, http://www.wordfrequency.info/files/entriesWithoutCollocates.txt (Rank 1 – 60000, every 7th word) would be adequate.
- Or come up with phrases and use either the phrase or the acronym of the phrase (“My website is my castle and I don’t intend to let you in to ransack” would be Mwimc&Iditlyi2r).
- Some sites offer to generate a password for you consisting of a randomized series of letters, numbers and symbols with characteristics they regard as secure. Password managers can do this too, see below.
- Single dictionary words are absolutely a no-no, even with character substitutions like p@$$w0rd.
- Don’t use any part of your name, email address, or any other information that could be known or googled about you, your business, your family or your pets.
- Don’t think that because you’re not rich and/or famous that you are not a target.
- Some sites are now offering biometric logins (fingerprints) for devices like iPhones and Androids – take the opportunity to safely make your life easier.
And now I hear you crying in despair that you’ll never be able to remember all that. Yeah. I know.
Use a password manager to improve password security, so you don’t have to remember all that
What are Password managers
They require that you remember one master password to open the manager and the manager remembers all your passwords. And credit card info, secure notes, bank account info, software licenses, and anything else that has to be ultra-secure but that you need to access. A good manager will help you generate random passwords so you don’t have to make them up. It saves a website’s password and will open the login page, fill in your credentials and log you in. It can record personal or professional info for forms and fill it in as necessary, based on multiple identities.
Cost of password managers
Some are free or freemium (with basic features free and more advanced, helpful features for a premium), some you pay per version (more the first time you purchase, less or nothing for upgrades), some are monthly or yearly subscriptions.
Which password manager
Here is a review of Life Hacker’s 5 Best Password Managers. The managers they review all have both Windows and Mac versions and are available for iDevices and Androids too. They vary in price starting from free/freemium. They include a variety of features, and most offer free trials.
My personal experience with password security and password managers
Personally I’ve used 1Password for close to 10 years.
- It has been in continual development, adding features and security.
- It uses AES-256 encryption which is absurdly strong encryption.
- Saves and fills login credentials for websites
- It’s available for macOS, iOS, Windows and Android, and can sync between all these devices.
- Generates both character random passwords and word random passwords of different lengths
- It’s now available in both a standalone version and in a cloud version by subscription more suitable for families and teams, that allow you to share your data with whom you want in the amount you want.
- It has a 30 day free trial.
I also use Last Pass in certain circumstances and have set up a number of clients with it, in its free version.
- The free version does not sync across devices
- But it is reliable, easy to use
- Generates random passwords for you, and
- Will save and fill passwords,
- Secure notes,
- Offers 2-factor authentication and generally make your data life significantly more secure.
- Their subscription improves on that with a shared family folder, unlimited device sync and other premium features.
You don’t have to do this all yourself
I would be happy to help you select a password manager and start to get your password life in order, as well as shore up other security features on your Mac, iPhone or iPad to better safeguard your life. Call 303 459 3363 for an appointment in the Boulder Colorado area.
For more information, here are some more resources.
Don’t Ignore It: The One Login That Ruins Every Other Password
Passwords – And why you should care – STOPzilla Blog
The Best Password Management Software of 2016
Review: The best password managers for PCs, Macs, and mobile devices
Best password manager apps for Mac: 1Password, LastPass, oneSafe, and more!
The Best Password Managers of 2016